In today’s digital economy, data centers house not just information—but the operational core of entire organizations. As cyber threats escalate and regulatory pressure increases, physical and digital security have become top priorities in data center design. But security isn’t just about alarms and cameras—it’s about smart, layered design strategies that prevent intrusion, protect assets, and ensure operational continuity.
This is where the role of architects becomes essential. Data center architects Stendel + Reich, for example, bring both technical fluency and spatial intelligence to these complex facilities—integrating security into the very fabric of the building without sacrificing functionality or performance.
Let’s explore how leading architects address security in the design of mission-critical data centers.
1. Site Selection with Risk Avoidance in Mind
Security starts before a shovel hits the ground. Architects assess multiple external risk factors, including:
- Distance from flood plains, seismic zones, or industrial hazards
- Proximity to roadways, airports, or public access points
- Redundancy of utilities and communication infrastructure
- Physical separation from nearby structures that could conceal threats
By selecting a low-risk site, architects build in a first layer of environmental and perimeter security.
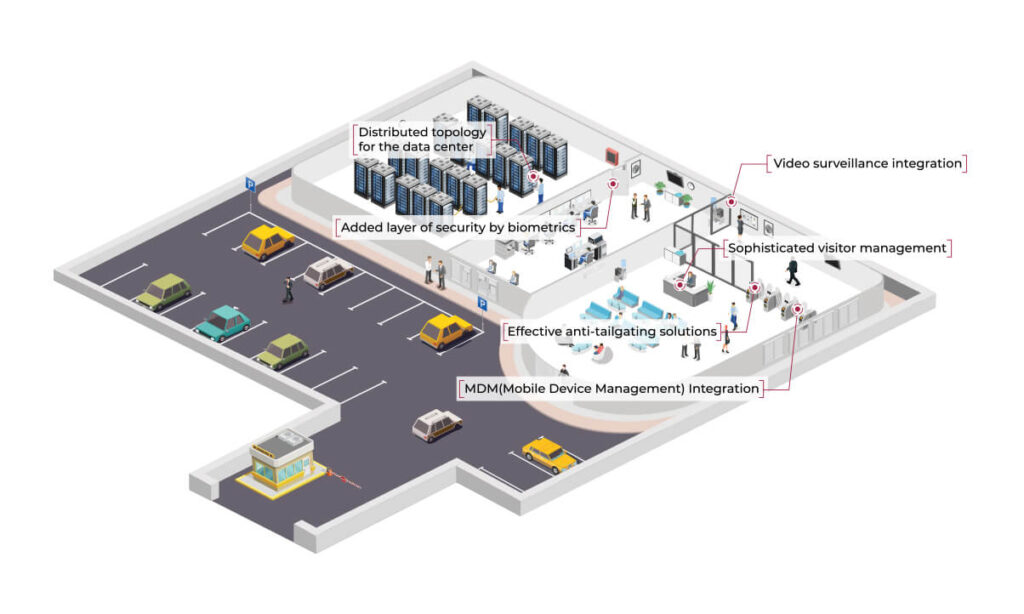
2. Controlled Perimeter and Secure Site Access
Once a site is chosen, architectural planning focuses on limiting unauthorized entry. This includes:
- Perimeter fencing with anti-climb features
- Limited and guarded entry points with access control systems
- Vehicle barriers and blast-resistant setbacks
- Integration of guard houses, gates, and CCTV coverage
Designers ensure all ingress and egress routes are monitored and manageable, with minimal blind spots.
3. Layered Building Access Controls
Inside the facility, architects design multiple zones of security to ensure that access becomes increasingly restricted:
- Mantraps at building entrances to control human flow
- Biometric or dual-authentication access points at key nodes
- Zoned entry to data halls, mechanical rooms, and admin areas
- Visitor management systems with real-time logging and restricted pathways
Each layer reduces the surface area for threats and limits access to only those with clearance.
4. Security Through Spatial Planning
Effective spatial design enhances security passively. Architects strategically:
- Separate operational and public-facing spaces
- Avoid dead-end corridors and concealment zones
- Design long sightlines to support surveillance
- Ensure room adjacencies support logical workflows without compromising security
They work closely with security consultants to embed access control into traffic flow.
5. Redundancy and Resilient Infrastructure
Beyond preventing unauthorized entry, architects plan for continuity in the event of breaches or system failures:
- Dual fiber pathways and redundant utility feeds
- Segregated electrical and network rooms
- Secure backup power systems with limited access
- Fire-resistant zones and blast-rated construction materials
Designing for compartmentalization ensures that one breach doesn’t compromise the entire facility.
6. Integration with Cybersecurity Systems
Though physical design is the focus, architects also support cybersecurity infrastructure by:
- Allocating secure spaces for firewall hardware, SOCs (Security Operations Centers), and NOCs
- Isolating data floors from administrative zones
- Supporting proper EMI shielding and cable security routing
- Designing climate-controlled environments for secure hardware longevity
Collaborating with IT and cybersecurity teams ensures architectural alignment with digital defenses.
Conclusion
In a world where data breaches can have catastrophic consequences, security is no longer an afterthought in data center design—it’s a core principle. By using spatial intelligence, layered access control, and resilient infrastructure planning, architects turn buildings into active participants in data protection.